在Ubuntu 9.10 / Debian Lenny上如何设置Apache2下的SSL Vhost
本文介绍如何在Ubuntu 9.10和Debian Lenny上的Apache2下设置SSL vhost,以便您可以通过HTTPS访问vhost(端口443)。 SSL是安全套接字层的缩写,是一种加密协议,通过端到端传输层加密网络连接段,为通过网络进行通信提供安全性。 我们在这里使用mod_ssl Apache模块,借助开源SSL工具包OpenSSL,通过SSL为Apache2提供强大的加密。
本文档不附带任何形式的保证! 我不会保证这将为您工作!
1初步说明
我假设你的Ubuntu 9.10或Debian Lenny框上有一个工作的LAMP设置,如这些教程所示:
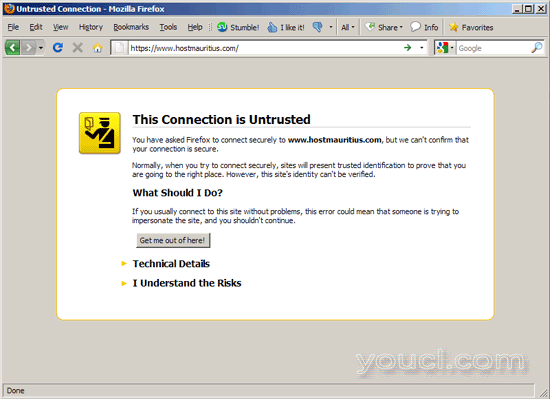
我将在本教程中为我的vhost www.hostmauritius.com设置SSL - hostmauritius.com是我拥有的一个域 - 将其替换为您自己的域。 我将演示如何使用自签名证书(这将导致浏览器警告当您访问http://www.hostmauritius.com )以及如何从受信任的证书颁发机构(CA)获取证书,如Verisign ,Thawte,Comodo等 - 使用来自受信任CA的证书,您的访问者将不会看到任何浏览器警告,就像自签名证书一样。 我将使用CAcert.org的证书 - 这些证书是免费的,但不被所有浏览器识别,但它应该提供如何从受信任的CA安装证书的想法。
重要的是要知道每个IP地址只能有一个SSL虚拟主机 - 如果要托管多个SSL vhost,则需要多个IP地址!
我使用root权限运行本教程中的所有步骤,因此请确保以root用户身份登录。 在Ubuntu上运行
sudo su
成为root用户。
2启用mod_ssl
要启用apache的SSL模块,请运行...
a2enmod ssl
...并重新启动Apache:
/etc/init.d/apache2 restart
Apache现在应该在端口443(HTTPS)上监听:
netstat -tap | grep https
root@server1:~# netstat -tap | grep https
tcp6 0 0 [::]:https [::]:* LISTEN 1238/apache2
root@server1:~#
3设置Vhost
我现在将使用文件根/var/www/www.hostmauritius.com创建vhost www.hostmauritius.com 。 首先我创建该目录:
mkdir /var/www/www.hostmauritius.com
Apache在文件/ etc / apache2 / sites-available / default-ssl中附带了默认的SSL vhost配置。 我们使用该文件作为www.hostmauritius.com vhost的模板...
cp /etc/apache2/sites-available/default-ssl /etc/apache2/sites-available/www.hostmauritius.com-ssl
...并打开/etc/apache2/sites-available/www.hostmauritius.com-ssl :
vi /etc/apache2/sites-available/www.hostmauritius.com-ssl
请确保在<VirtualHost xxx.xxx.xxx.xxx:443>行(本例中为192.168.0.100)中使用正确的IP地址; 还要填写正确的ServerAdmin电子邮件地址并添加ServerName行。 如果需要,请调整DocumentRoot行和<Directory>指令中的路径。
<IfModule mod_ssl.c>
<VirtualHost 192.168.0.100:443>
ServerAdmin webmaster@hostmauritius.com
ServerName www.hostmauritius.com:443
DocumentRoot /var/www/www.hostmauritius.com
<Directory />
Options FollowSymLinks
AllowOverride None
</Directory>
<Directory /var/www/www.hostmauritius.com/>
Options Indexes FollowSymLinks MultiViews
AllowOverride None
Order allow,deny
allow from all
</Directory>
ScriptAlias /cgi-bin/ /usr/lib/cgi-bin/
<Directory "/usr/lib/cgi-bin">
AllowOverride None
Options +ExecCGI -MultiViews +SymLinksIfOwnerMatch
Order allow,deny
Allow from all
</Directory>
ErrorLog /var/log/apache2/error.log
# Possible values include: debug, info, notice, warn, error, crit,
# alert, emerg.
LogLevel warn
CustomLog /var/log/apache2/ssl_access.log combined
Alias /doc/ "/usr/share/doc/"
<Directory "/usr/share/doc/">
Options Indexes MultiViews FollowSymLinks
AllowOverride None
Order deny,allow
Deny from all
Allow from 127.0.0.0/255.0.0.0 ::1/128
</Directory>
# SSL Engine Switch:
# Enable/Disable SSL for this virtual host.
SSLEngine on
# A self-signed (snakeoil) certificate can be created by installing
# the ssl-cert package. See
# /usr/share/doc/apache2.2-common/README.Debian.gz for more info.
# If both key and certificate are stored in the same file, only the
# SSLCertificateFile directive is needed.
SSLCertificateFile /etc/ssl/certs/ssl-cert-snakeoil.pem
SSLCertificateKeyFile /etc/ssl/private/ssl-cert-snakeoil.key
# Server Certificate Chain:
# Point SSLCertificateChainFile at a file containing the
# concatenation of PEM encoded CA certificates which form the
# certificate chain for the server certificate. Alternatively
# the referenced file can be the same as SSLCertificateFile
# when the CA certificates are directly appended to the server
# certificate for convinience.
#SSLCertificateChainFile /etc/apache2/ssl.crt/server-ca.crt
# Certificate Authority (CA):
# Set the CA certificate verification path where to find CA
# certificates for client authentication or alternatively one
# huge file containing all of them (file must be PEM encoded)
# Note: Inside SSLCACertificatePath you need hash symlinks
# to point to the certificate files. Use the provided
# Makefile to update the hash symlinks after changes.
#SSLCACertificatePath /etc/ssl/certs/
#SSLCACertificateFile /etc/apache2/ssl.crt/ca-bundle.crt
# Certificate Revocation Lists (CRL):
# Set the CA revocation path where to find CA CRLs for client
# authentication or alternatively one huge file containing all
# of them (file must be PEM encoded)
# Note: Inside SSLCARevocationPath you need hash symlinks
# to point to the certificate files. Use the provided
# Makefile to update the hash symlinks after changes.
#SSLCARevocationPath /etc/apache2/ssl.crl/
#SSLCARevocationFile /etc/apache2/ssl.crl/ca-bundle.crl
# Client Authentication (Type):
# Client certificate verification type and depth. Types are
# none, optional, require and optional_no_ca. Depth is a
# number which specifies how deeply to verify the certificate
# issuer chain before deciding the certificate is not valid.
#SSLVerifyClient require
#SSLVerifyDepth 10
# Access Control:
# With SSLRequire you can do per-directory access control based
# on arbitrary complex boolean expressions containing server
# variable checks and other lookup directives. The syntax is a
# mixture between C and Perl. See the mod_ssl documentation
# for more details.
#<Location />
#SSLRequire ( %{SSL_CIPHER} !~ m/^(EXP|NULL)/ \
# and %{SSL_CLIENT_S_DN_O} eq "Snake Oil, Ltd." \
# and %{SSL_CLIENT_S_DN_OU} in {"Staff", "CA", "Dev"} \
# and %{TIME_WDAY} >= 1 and %{TIME_WDAY} <= 5 \
# and %{TIME_HOUR} >= 8 and %{TIME_HOUR} <= 20 ) \
# or %{REMOTE_ADDR} =~ m/^192\.76\.162\.[0-9]+$/
#</Location>
# SSL Engine Options:
# Set various options for the SSL engine.
# o FakeBasicAuth:
# Translate the client X.509 into a Basic Authorisation. This means that
# the standard Auth/DBMAuth methods can be used for access control. The
# user name is the `one line' version of the client's X.509 certificate.
# Note that no password is obtained from the user. Every entry in the user
# file needs this password: `xxj31ZMTZzkVA'.
# o ExportCertData:
# This exports two additional environment variables: SSL_CLIENT_CERT and
# SSL_SERVER_CERT. These contain the PEM-encoded certificates of the
# server (always existing) and the client (only existing when client
# authentication is used). This can be used to import the certificates
# into CGI scripts.
# o StdEnvVars:
# This exports the standard SSL/TLS related `SSL_*' environment variables.
# Per default this exportation is switched off for performance reasons,
# because the extraction step is an expensive operation and is usually
# useless for serving static content. So one usually enables the
# exportation for CGI and SSI requests only.
# o StrictRequire:
# This denies access when "SSLRequireSSL" or "SSLRequire" applied even
# under a "Satisfy any" situation, i.e. when it applies access is denied
# and no other module can change it.
# o OptRenegotiate:
# This enables optimized SSL connection renegotiation handling when SSL
# directives are used in per-directory context.
#SSLOptions +FakeBasicAuth +ExportCertData +StrictRequire
<FilesMatch "\.(cgi|shtml|phtml|php)$">
SSLOptions +StdEnvVars
</FilesMatch>
<Directory /usr/lib/cgi-bin>
SSLOptions +StdEnvVars
</Directory>
# SSL Protocol Adjustments:
# The safe and default but still SSL/TLS standard compliant shutdown
# approach is that mod_ssl sends the close notify alert but doesn't wait for
# the close notify alert from client. When you need a different shutdown
# approach you can use one of the following variables:
# o ssl-unclean-shutdown:
# This forces an unclean shutdown when the connection is closed, i.e. no
# SSL close notify alert is send or allowed to received. This violates
# the SSL/TLS standard but is needed for some brain-dead browsers. Use
# this when you receive I/O errors because of the standard approach where
# mod_ssl sends the close notify alert.
# o ssl-accurate-shutdown:
# This forces an accurate shutdown when the connection is closed, i.e. a
# SSL close notify alert is send and mod_ssl waits for the close notify
# alert of the client. This is 100% SSL/TLS standard compliant, but in
# practice often causes hanging connections with brain-dead browsers. Use
# this only for browsers where you know that their SSL implementation
# works correctly.
# Notice: Most problems of broken clients are also related to the HTTP
# keep-alive facility, so you usually additionally want to disable
# keep-alive for those clients, too. Use variable "nokeepalive" for this.
# Similarly, one has to force some clients to use HTTP/1.0 to workaround
# their broken HTTP/1.1 implementation. Use variables "downgrade-1.0" and
# "force-response-1.0" for this.
BrowserMatch ".*MSIE.*" \
nokeepalive ssl-unclean-shutdown \
downgrade-1.0 force-response-1.0
</VirtualHost>
</IfModule> |
如您所见,此vhost使用Ubuntu / Debian附带的默认自签名snakeoil证书:
SSLCertificateFile /etc/ssl/certs/ssl-cert-snakeoil.pem
SSLCertificateKeyFile /etc/ssl/private/ssl-cert-snakeoil.key
现在禁用默认SSL vhost(如果启用),启用www.hostmauritius.com vhost并重新加载apache:
a2dissite default-ssl
a2ensite www.hostmauritius.com-ssl
/etc/init.d/apache2 reload
现在打开浏览器并转到您的新SSL vhost(在这种情况下为https://www.hostmauritius.com )。 因为我们使用Debian / Ubuntu的默认自签名证书,所以我们应该收到一个警告,指出连接是不受信任的(使用该网站,点击我了解风险并按照浏览器中的说明进行操作):
4创建自签名证书
到目前为止,我们已经使用了Debian / Ubuntu的默认自签名证书。 现在我将向您展示如何创建自己的自签名证书。 使用此证书,您仍然会收到浏览器警告,但是此证书需要稍后从受信任的CA获取受信任的证书。
确保安装了ssl-cert软件包:
aptitude install ssl-cert
您现在可以为www.hostmauritius.com创建一个自签名证书,如下所示:
make-ssl-cert /usr/share/ssl-cert/ssleay.cnf /etc/ssl/private/www.hostmauritius.com.crt
您将被要求提供主机名:
主机名: < - www.hostmauritius.com
这将在一个文件中创建自签名证书和私钥,/ etc/ssl/private/www.hostmauritius.com.crt :
cat /etc/ssl/private/www.hostmauritius.com.crt
-----BEGIN RSA PRIVATE KEY----- MIICXgIBAAKBgQDWuQUCXjDucCdKnowwclux0Tb392+I/KSLkqp4bY577U4EcS0V J28eWIYOTiA38UDteLMXZSFyzWtq1QREzU0sPeQXWjJ/r6sDGSNlOFxnBJlg/ll2 2JHTeMZQZ4QoLejaS8SBU2v8mQFIZrvT+/RUsAyFNVvfVA+dm5bQS9dH5QIDAQAB AoGBAMBwsfydTl1kRtKpphsFYwjK6Ojz6hJr20z79axZBAotdG6mwDDlVsFrtTm8 60M4BWjPdDLTgFbTpCHrKBhBp5cJqgSXntd2i2JjOFpIQSlinGJ6HncFEC3AAxeE PVTH77k2sVckwQ5tnOVX6gGuYt5E5wd3J43mLyyHCpFXz4dBAkEA/O4q2CpCXlT0 Mklt/8rlzzIhxyoOuPI3WH+lr5tO3LSNpLbzW74l/lTvFhCbQCKsb3eyZVhzE+f+ 9ZJM+ao5kwJBANlUJPyc2bYpY2124c83rYtK6Xth9c+sxxUdWbkkyEdaF1ixlR+r 8Qoze+ISHBr9DCZWbQGZirwoX/+qufvFA6cCQHECcT44U4MWbi1xxaY+n8Od4J2+ Wumjv7rY/cyile/i9E6eN8nMAenLRTAUp2lWlLkRQDIr/O7t/2r1vVLoDeUCQQCO 5R+opS0U9CO27srMZ+yIwMnB4Ygxc4Y24OSEsqWpHJhrLeBCQdir/2v+GjA2oplh f8QOoDkzPEzamxPMch7TAkEAyLke88CR1awZQQnTGKho6g5npdGgntjBVO+ZEl18 PfCIyGk5bsLrAsprgS+Xp5SSQfAG2fUatpXqsYGBO8q2dA== -----END RSA PRIVATE KEY----- -----BEGIN CERTIFICATE----- MIIBqzCCARQCCQDDCFjQ7Ii1gjANBgkqhkiG9w0BAQUFADAaMRgwFgYDVQQDEw93 d3cuZXhhbXBsZS5jb20wHhcNMTAwMTEyMTY1NDI2WhcNMjAwMTEwMTY1NDI2WjAa MRgwFgYDVQQDEw93d3cuZXhhbXBsZS5jb20wgZ8wDQYJKoZIhvcNAQEBBQADgY0A MIGJAoGBANa5BQJeMO5wJ0qejDByW7HRNvf3b4j8pIuSqnhtjnvtTgRxLRUnbx5Y hg5OIDfxQO14sxdlIXLNa2rVBETNTSw95BdaMn+vqwMZI2U4XGcEmWD+WXbYkdN4 xlBnhCgt6NpLxIFTa/yZAUhmu9P79FSwDIU1W99UD52bltBL10flAgMBAAEwDQYJ KoZIhvcNAQEFBQADgYEAJ/tYRc3CImo2c4FyG+UJTUIgu+p8IcMH9egGaMc335a5 IwA2BBsiS3YAux8mteE2N03Nae6wTVbgEl8J68z1XyzklGtC/EG7ygtnOlfFTJWn U5HMaGOGBvOnFViF4e/DuBs7VPePKzqF2mmKIeAvoMA5GTH/iA4yJIFlgHhCMU8= -----END CERTIFICATE----- |
我现在将该文件分成两部分,私钥/etc/ssl/private/www.hostmauritius.com.key和自签名证书/etc/ssl/certs/www.hostmauritius.com.pem :
vi /etc/ssl/private/www.hostmauritius.com.key
该文件必须包含以----- BEGIN RSA PRIVATE KEY -----开始的部分,以----- END RSA PRIVATE KEY结尾----- :
-----BEGIN RSA PRIVATE KEY----- MIICXgIBAAKBgQDWuQUCXjDucCdKnowwclux0Tb392+I/KSLkqp4bY577U4EcS0V J28eWIYOTiA38UDteLMXZSFyzWtq1QREzU0sPeQXWjJ/r6sDGSNlOFxnBJlg/ll2 2JHTeMZQZ4QoLejaS8SBU2v8mQFIZrvT+/RUsAyFNVvfVA+dm5bQS9dH5QIDAQAB AoGBAMBwsfydTl1kRtKpphsFYwjK6Ojz6hJr20z79axZBAotdG6mwDDlVsFrtTm8 60M4BWjPdDLTgFbTpCHrKBhBp5cJqgSXntd2i2JjOFpIQSlinGJ6HncFEC3AAxeE PVTH77k2sVckwQ5tnOVX6gGuYt5E5wd3J43mLyyHCpFXz4dBAkEA/O4q2CpCXlT0 Mklt/8rlzzIhxyoOuPI3WH+lr5tO3LSNpLbzW74l/lTvFhCbQCKsb3eyZVhzE+f+ 9ZJM+ao5kwJBANlUJPyc2bYpY2124c83rYtK6Xth9c+sxxUdWbkkyEdaF1ixlR+r 8Qoze+ISHBr9DCZWbQGZirwoX/+qufvFA6cCQHECcT44U4MWbi1xxaY+n8Od4J2+ Wumjv7rY/cyile/i9E6eN8nMAenLRTAUp2lWlLkRQDIr/O7t/2r1vVLoDeUCQQCO 5R+opS0U9CO27srMZ+yIwMnB4Ygxc4Y24OSEsqWpHJhrLeBCQdir/2v+GjA2oplh f8QOoDkzPEzamxPMch7TAkEAyLke88CR1awZQQnTGKho6g5npdGgntjBVO+ZEl18 PfCIyGk5bsLrAsprgS+Xp5SSQfAG2fUatpXqsYGBO8q2dA== -----END RSA PRIVATE KEY----- |
密钥只能由root可读写:
chmod 600 /etc/ssl/private/www.hostmauritius.com.key
vi /etc/ssl/certs/www.hostmauritius.com.pem
该文件必须包含以-----开始证书-----开头的部分,并以----- END CERTIFICATE -----结尾:
-----BEGIN CERTIFICATE----- MIIBqzCCARQCCQDDCFjQ7Ii1gjANBgkqhkiG9w0BAQUFADAaMRgwFgYDVQQDEw93 d3cuZXhhbXBsZS5jb20wHhcNMTAwMTEyMTY1NDI2WhcNMjAwMTEwMTY1NDI2WjAa MRgwFgYDVQQDEw93d3cuZXhhbXBsZS5jb20wgZ8wDQYJKoZIhvcNAQEBBQADgY0A MIGJAoGBANa5BQJeMO5wJ0qejDByW7HRNvf3b4j8pIuSqnhtjnvtTgRxLRUnbx5Y hg5OIDfxQO14sxdlIXLNa2rVBETNTSw95BdaMn+vqwMZI2U4XGcEmWD+WXbYkdN4 xlBnhCgt6NpLxIFTa/yZAUhmu9P79FSwDIU1W99UD52bltBL10flAgMBAAEwDQYJ KoZIhvcNAQEFBQADgYEAJ/tYRc3CImo2c4FyG+UJTUIgu+p8IcMH9egGaMc335a5 IwA2BBsiS3YAux8mteE2N03Nae6wTVbgEl8J68z1XyzklGtC/EG7ygtnOlfFTJWn U5HMaGOGBvOnFViF4e/DuBs7VPePKzqF2mmKIeAvoMA5GTH/iA4yJIFlgHhCMU8= -----END CERTIFICATE----- |
现在我们可以删除/etc/ssl/private/www.hostmauritius.com.crt文件:
rm -f /etc/ssl/private/www.hostmauritius.com.crt
接下来,我们调整我们的SSL vhost以使用新的私钥和自签名证书:
vi /etc/apache2/sites-available/www.hostmauritius.com-ssl
[...]
# A self-signed (snakeoil) certificate can be created by installing
# the ssl-cert package. See
# /usr/share/doc/apache2.2-common/README.Debian.gz for more info.
# If both key and certificate are stored in the same file, only the
# SSLCertificateFile directive is needed.
SSLCertificateFile /etc/ssl/certs/www.hostmauritius.com.pem
SSLCertificateKeyFile /etc/ssl/private/www.hostmauritius.com.key
[...] |
重新加载Apache:
/etc/init.d/apache2 reload
SSL vhost现在将使用您的新私钥和自签名证书进行加密(但是由于它是一个自签名证书,当您访问https://www.hostmauritius.com时,您仍然会收到浏览器的警告)。








