从版本4.0开始,Samba能够作为Active Directory(AD)域控制器(DC)运行。 在本教程中,我将介绍如何使用Windows 10,CentOS 7和CentOS 6客户端将Samba 4配置为域控制器。
我将使用3系统,一个CentOS 7服务器和一个用于远程管理的Windows 10客户端,CentOS 7和CentOS 6客户端。
- 192.168.1.190 Samba4 AD centos7
- 192.168.1.191远程管理赢10
- 192.168.1.22 - 客户端认证 - 中心7
- 192.168.1.192 - 客户端验证 - centos 6
安装Samba 4
192.168.1.190 Samba4 AD centos 7
Basis是一个CentOS 7,安装最少,SELinux已禁用。
[root@samba4 ~]# sestatus
SELinux status: disabled
[root@samba4 ~]#
在/ etc / hosts文件中创建一个条目。
[root@samba4 ~]# cat /etc/hosts
127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4
::1 localhost localhost.localdomain localhost6 localhost6.localdomain6
192.168.1.190 samba4.sunil.cc samba4
[root@samba4 ~]#
安装epel repo。
[root@samba4 ~]# yum install epel-release -y
安装编译samba4所需的所有软件包。
[root@samba4 ~]# yum install perl gcc libacl-devel libblkid-devel gnutls-devel readline-devel python-devel gdb pkgconfig krb5-workstation zlib-devel setroubleshoot-server libaio-devel setroubleshoot-plugins\ policycoreutils-python libsemanage-python setools-libs-python setools-libs popt-devel libpcap-devel sqlite-devel libidn-devel libxml2-devel libacl-devel libsepol-devel libattr-devel keyutils-libs-devel\ cyrus-sasl-devel cups-devel bind-utils libxslt docbook-style-xsl openldap-devel pam-devel bzip2 vim wget -y
现在下载samba4包。 我使用samba-4.6.0这是最新的在这个设置。
[root@samba4 ~]# wget https://download.samba.org/pub/samba/stable/samba-4.6.0.tar.gz
现在让我们安装samba4。
[root@samba4 ~]# tar -zxvf samba-4.6.0.tar.gz [root@samba4 ~]# cd samba-4.6.0 [root@samba4 samba-4.6.0]# ./configure --enable-debug --enable-selftest --with-ads --with-systemd --with-winbind [root@samba4 samba-4.6.0]# make && make install
根据系统速度,安装大约需要10分钟。
现在我们将进行域配置。
[root@samba4 samba]# samba-tool domain provision --use-rfc2307 --interactive
Realm [SUNIL.CC]:
Domain [SUNIL]:
Server Role (dc, member, standalone) [dc]: dc
DNS backend (SAMBA_INTERNAL, BIND9_FLATFILE, BIND9_DLZ, NONE) [SAMBA_INTERNAL]:
DNS forwarder IP address (write 'none' to disable forwarding) [4.2.2.1]:
Administrator password:
Retype password:
Looking up IPv4 addresses
Looking up IPv6 addresses
No IPv6 address will be assigned
Setting up share.ldb
Setting up secrets.ldb
Setting up the registry
Setting up the privileges database
Setting up idmap db
Setting up SAM db
Setting up sam.ldb partitions and settings
Setting up sam.ldb rootDSE
Pre-loading the Samba 4 and AD schema
Adding DomainDN: DC=sunil,DC=cc
Adding configuration container
Setting up sam.ldb schema
Setting up sam.ldb configuration data
Setting up display specifiers
Modifying display specifiers
Adding users container
Modifying users container
Adding computers container
Modifying computers container
Setting up sam.ldb data
Setting up well known security principals
Setting up sam.ldb users and groups
ERROR(ldb): uncaught exception - operations error at ../source4/dsdb/samdb/ldb_modules/password_hash.c:2820
File "/usr/local/samba/lib64/python2.7/site-packages/samba/netcmd/__init__.py", line 176, in _run
return self.run(*args, **kwargs)
File "/usr/local/samba/lib64/python2.7/site-packages/samba/netcmd/domain.py", line 471, in run
nosync=ldap_backend_nosync, ldap_dryrun_mode=ldap_dryrun_mode)
File "/usr/local/samba/lib64/python2.7/site-packages/samba/provision/__init__.py", line 2175, in provision
skip_sysvolacl=skip_sysvolacl)
File "/usr/local/samba/lib64/python2.7/site-packages/samba/provision/__init__.py", line 1787, in provision_fill
next_rid=next_rid, dc_rid=dc_rid)
File "/usr/local/samba/lib64/python2.7/site-packages/samba/provision/__init__.py", line 1447, in fill_samdb
"KRBTGTPASS_B64": b64encode(krbtgtpass.encode('utf-16-le'))
File "/usr/local/samba/lib64/python2.7/site-packages/samba/provision/common.py", line 55, in setup_add_ldif
ldb.add_ldif(data, controls)
File "/usr/local/samba/lib64/python2.7/site-packages/samba/__init__.py", line 225, in add_ldif
self.add(msg, controls)
[root@samba4 samba]#
当我们提供域时会有一些错误。
要修复它们,请在/etc/krb5.conf中注释掉下面的一行。
-------- #includedir /etc/krb5.conf.d/ --------
再次运行域配置,现在域将被创建没有错误。
[root@samba4 etc]# samba-tool domain provision --use-rfc2307 --interactive Realm [SUNIL.CC]: Domain [SUNIL]: Server Role (dc, member, standalone) [dc]: DNS backend (SAMBA_INTERNAL, BIND9_FLATFILE, BIND9_DLZ, NONE) [SAMBA_INTERNAL]: DNS forwarder IP address (write 'none' to disable forwarding) [4.2.2.1]: Administrator password: Retype password: Looking up IPv4 addresses Looking up IPv6 addresses No IPv6 address will be assigned Setting up secrets.ldb Setting up the registry Setting up the privileges database Setting up idmap db Setting up SAM db Setting up sam.ldb partitions and settings Setting up sam.ldb rootDSE Pre-loading the Samba 4 and AD schema Adding DomainDN: DC=sunil,DC=cc Adding configuration container Setting up sam.ldb schema Setting up sam.ldb configuration data Setting up display specifiers Modifying display specifiers Adding users container Modifying users container Adding computers container Modifying computers container Setting up sam.ldb data Setting up well known security principals Setting up sam.ldb users and groups Setting up self join Adding DNS accounts Creating CN=MicrosoftDNS,CN=System,DC=sunil,DC=cc Creating DomainDnsZones and ForestDnsZones partitions Populating DomainDnsZones and ForestDnsZones partitions Setting up sam.ldb rootDSE marking as synchronized Fixing provision GUIDs A Kerberos configuration suitable for Samba AD has been generated at /usr/local/samba/private/krb5.conf Setting up fake yp server settings Once the above files are installed, your Samba4 server will be ready to use Server Role: active directory domain controller Hostname: samba4 NetBIOS Domain: SUNIL DNS Domain: sunil.cc DOMAIN SID: S-1-5-21-2936486394-2075362935-551615353 [root@samba4 etc]#
确保端口在防火墙中打开。
[root@samba4 etc]#firewall-cmd --add-port=53/tcp --permanent;firewall-cmd --add-port=53/udp --permanent;firewall-cmd --add-port=88/tcp --permanent;firewall-cmd --add-port=88/udp --permanent; \ firewall-cmd --add-port=135/tcp --permanent;firewall-cmd --add-port=137-138/udp --permanent;firewall-cmd --add-port=139/tcp --permanent; \ firewall-cmd --add-port=389/tcp --permanent;firewall-cmd --add-port=389/udp --permanent;firewall-cmd --add-port=445/tcp --permanent; \ firewall-cmd --add-port=464/tcp --permanent;firewall-cmd --add-port=464/udp --permanent;firewall-cmd --add-port=636/tcp --permanent; \ firewall-cmd --add-port=1024-5000/tcp --permanent;firewall-cmd --add-port=3268-3269/tcp --permanent [root@samba4 ~]# firewall-cmd --reload
创建启动脚本以在重新启动期间自动启动服务。
[root@samba4 ~]# cat /etc/systemd/system/samba.service [Unit] Description= Samba 4 Active Directory After=syslog.target After=network.target [Service] Type=forking PIDFile=/usr/local/samba/var/run/samba.pid ExecStart=/usr/local/samba/sbin/samba [Install] WantedBy=multi-user.target [root@samba4 ~]# [root@samba4 ~]# systemctl enable samba Created symlink from /etc/systemd/system/multi-user.target.wants/samba.service to /etc/systemd/system/samba.service. [root@samba4 ~]# systemctl start samba
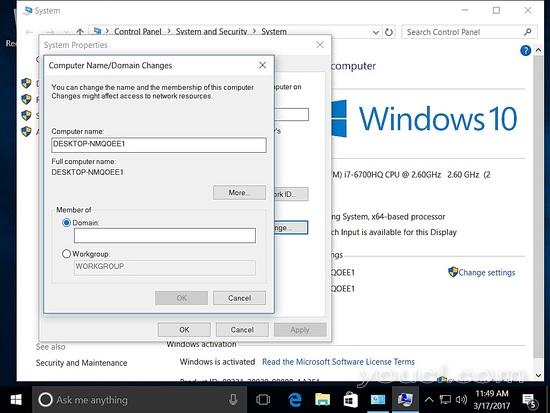
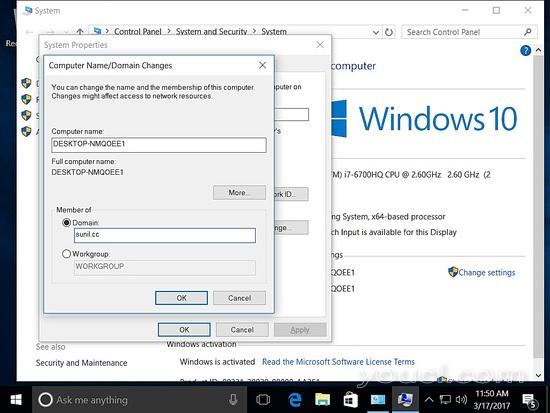
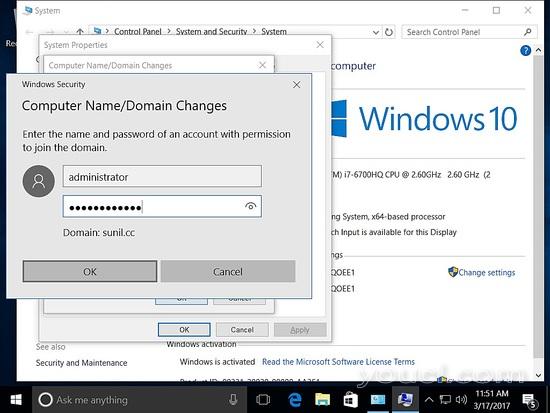
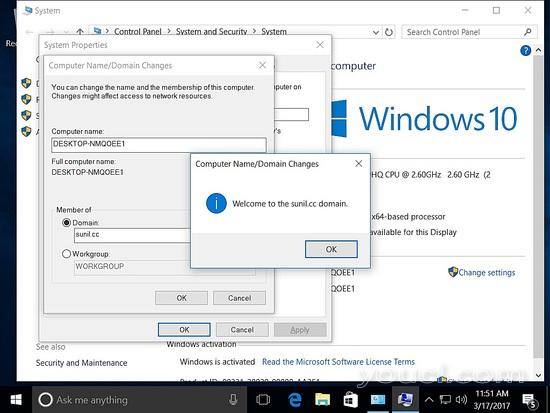
将Windows主机添加到域
192.168.1.191远程管理赢10
确保主机添加了静态ipaddress。
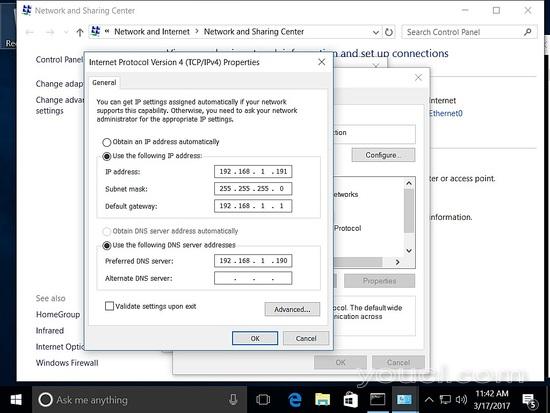
将主机添加到域中。
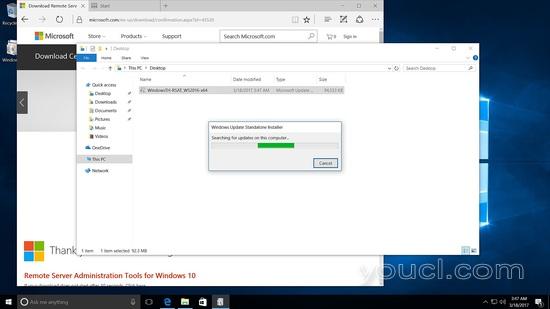
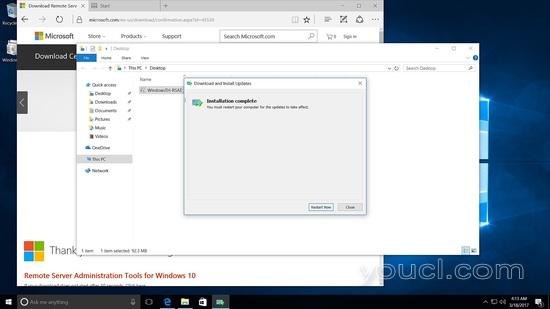
要从Windows管理Samba4,我们需要安装Microsoft Remote Server Tools(RSAT)。
wiki页面具有https://wiki.samba.org/index.php/Installing_RSAT的链接
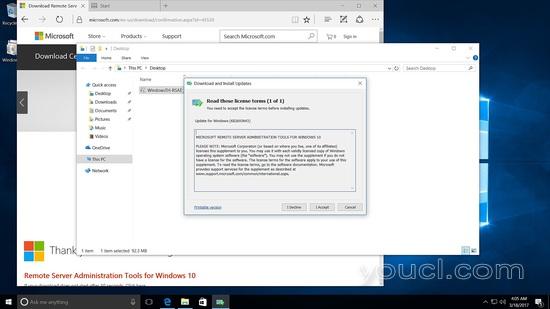
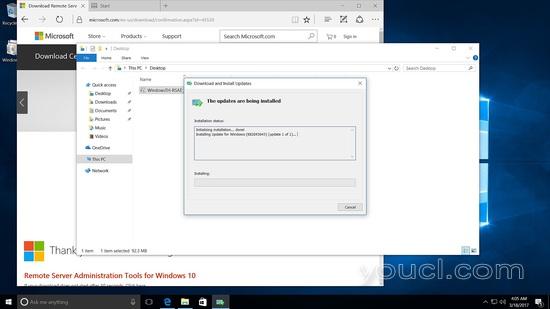
在Windows 10中安装RSAT工具
运行安装程序
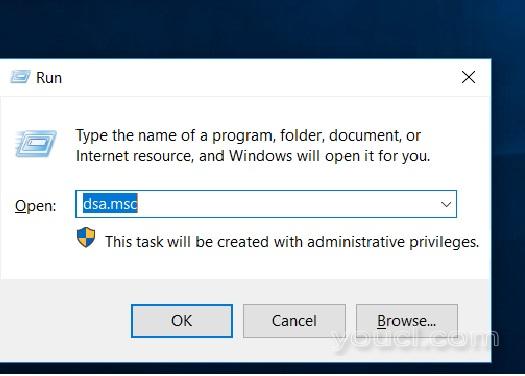
重新启动后运行并输入dsa.msc
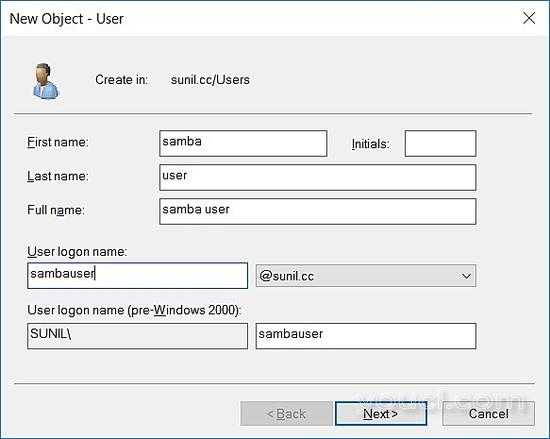
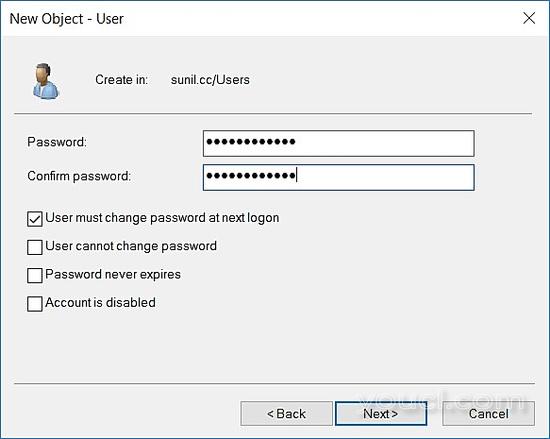
点击sunil.cc域,右键单击新建 - >用户。
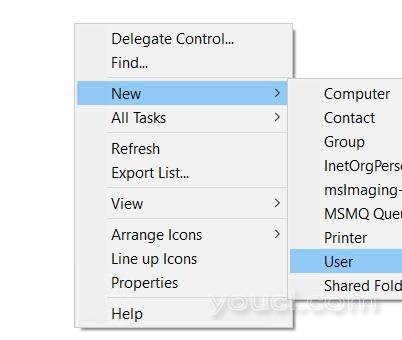
创建测试用户。
在CentOS 7上使用Samba 4进行客户端认证
192.168.1.22 - CentOS 7上的客户端认证
安装包:
[root@centos7 ~]# yum -y install realmd sssd oddjob oddjob-mkhomedir adcli samba-common
检查与samba4的连接:
[root@centos7 ~]# realm discover SUNIL.CC sunil.cc type: kerberos realm-name: SUNIL.CC domain-name: sunil.cc configured: kerberos-member server-software: active-directory client-software: sssd required-package: oddjob required-package: oddjob-mkhomedir required-package: sssd required-package: adcli required-package: samba-common-tools login-formats: %U login-policy: allow-realm-logins [root@centos7 ~]#
加入域名
[root@centos7 ~]# realm join SUNIL.CC Password for Administrator: [root@centos7 ~]#
检查我们是否能够从samba4获取用户。
[root@centos7 ~]# id SUNIL\\testuser uid=1570001104(testuser@sunil.cc) gid=1570000513(domain users@sunil.cc) groups=1570000513(domain users@sunil.cc) [root@centos7 ~]#
配置sssd
[root@centos7 ~]# cat /etc/sssd/sssd.conf [sssd] domains = sunil.cc config_file_version = 2 services = nss, pam [domain/sunil.cc] ad_domain = sunil.cc krb5_realm = SUNIL.CC realmd_tags = manages-system joined-with-samba cache_credentials = True id_provider = ad krb5_store_password_if_offline = True default_shell = /bin/bash ldap_id_mapping = True use_fully_qualified_names = True fallback_homedir = /home/%u@%d access_provider = ad [root@centos7 ~]#
重新启动sssd。
[root@centos7 ~]# systemctl restart sssd [root@centos7 ~]# systemctl enable sssd
检查用户。
[root@centos7 ~]# id sambauser@sunil.cc uid=1570001105(sambauser@sunil.cc) gid=1570000513(domain users@sunil.cc) groups=1570000513(domain users@sunil.cc),1570000512(domain admins@sunil.cc),1570000572(denied rodc password replication group@sunil.cc) [root@centos7 ~]#
获取没有域名的用户。
[root@centos7 ~]# vim /etc/sssd/sssd.conf ----------- ------------ use_fully_qualified_names = False ----------- -----------
重新启动sssd和check id命令。
[root@centos7 ~]# systemctl restart sssd [root@centos7 ~]# id sambauser uid=1570001105(sambauser) gid=1570000513(domain users) groups=1570000513(domain users),1570000512(domain admins),1570000572(denied rodc password replication group) [root@centos7 ~]#
在CentOS 6上使用Samba 4进行客户端身份验证
192.168.1.192 - CentOS 6上的客户端认证。
安装包装。
[root@centos6 db]# yum install pam pam_ldap pam_krb5 sssd sssd-ldap sssd-common authconfig oddjob oddjob-mkhomedir openldap openldap-clients krb5-workstation adcli -y
更改kerberos配置文件。
[root@centos6 db]# cat /etc/krb5.conf
[logging]
default = FILE:/var/log/krb5libs.log
kdc = FILE:/var/log/krb5kdc.log
admin_server = FILE:/var/log/kadmind.log
[libdefaults]
default_realm = SUNIL.CC
dns_lookup_realm = false
dns_lookup_kdc = false
ticket_lifetime = 24h
renew_lifetime = 7d
forwardable = true
[realms]
SUNIL.CC = {
kdc = samba4.sunil.cc
admin_server = samba4.sunil.cc
}
[domain_realm]
.sunil.cc = SUNIL.CC
sunil.cc = SUNIL.CC
[root@centos6 db]#
我们将使用adcli命令加入域。
[root@centos6 db]# adcli info sunil.cc [domain] domain-name = sunil.cc domain-short = SUNIL domain-forest = sunil.cc domain-controller = samba4.sunil.cc domain-controller-site = Default-First-Site-Name domain-controller-flags = pdc gc ldap ds kdc timeserv closest writable good-timeserv full-secret domain-controller-usable = yes domain-controllers = samba4.sunil.cc [computer] computer-site = Default-First-Site-Name [root@centos6 db]# [root@centos6 db]# adcli join sunil.cc Password for Administrator@SUNIL.CC: [root@centos6 db]#
确保创建了kerberos票证。
[root@centos6 db]# klist -ke
配置认证
[root@centos6 db]# authconfig --enablesssd --enablesssdauth --enablemkhomedir --update
现在修改sssd配置来进行身份验证。
[root@centos6 db]# cat /etc/sssd/sssd.conf [sssd] services = nss, pam, ssh, autofs config_file_version = 2 domains = sunil.cc [domain/sunil.cc] id_provider = ad # Uncomment if service discovery is not working # ad_server = server.win.example.com default_shell = /bin/bash fallback_homedir = /home/%u [root@centos6 db]#
重新启动sssd服务。
[root@centos6 db]# chkconfig sssd on [root@centos6 db]# service sssd restart Stopping sssd: [ OK ] Starting sssd: [ OK ] [root@centos6 db]#
验证用户
[root@centos6 db]# id sambauser uid=1570001105(sambauser) gid=1570000513(domain users) groups=1570000513(domain users),1570000512(domain admins),1570000572(denied rodc password replication group) [root@centos6 db]#








